When it comes to WordPress security, it’s not unusual for many to simply install a security plugin and call it a day, thinking that their site is now completely secure.
But, a plugin for improved security often makes your site very sluggish, is not a complete solution for security and might also give you a false sense of security.
Your site is only as security as its weakest link, that’s why it’s important that you consider the whole picture and that you try to improve as many security aspects as possible.
In this article we’ve collected a list of different measurements that are easy for anyone to implement and that can improve your site’s security a lot.
Table of content:
- Is WordPress secure?
- 1 – Keep WordPress, plugins and themes up to date
- 2 – Uninstall inactive plugins and themes
- 3 – Use the right (restrictive) file permissions
- 4 – Disable the built-in file editor
- 5 – Set a custom database prefix
- 6 – Use strong usernames and passwords
- 7 – Implement 2FA (Two-Factor Authentication)
- 8 – Change security keys in wp-config.php
- 9 – Disable XML-RPC
- 10 – Hide what WordPress version you are using
- 11 – Use SSL and HTTPS
- 12 – Change WP Admin URL
- 13 – Make sure to take daily backups
- 14 – Choose a secure hosting solution
- Final words
Is WordPress secure?
Yes! at the core, WordPress is very secure, but it is also very much your own responsibility for exactly how secure your website will be in the end.
WordPress has a very rigorous quality and security control and is often very quick to fix any vulnerability that are discovered. This means that if you are able to keep your WordPress installation up to date, there is very little risk that your website will ever be “hacked” because of WordPress itself.
The most common reason behind intrusion on one’s website is instead that the administrator has somehow neglected security, and has not followed all the advice that is available on how to keep his website safe.

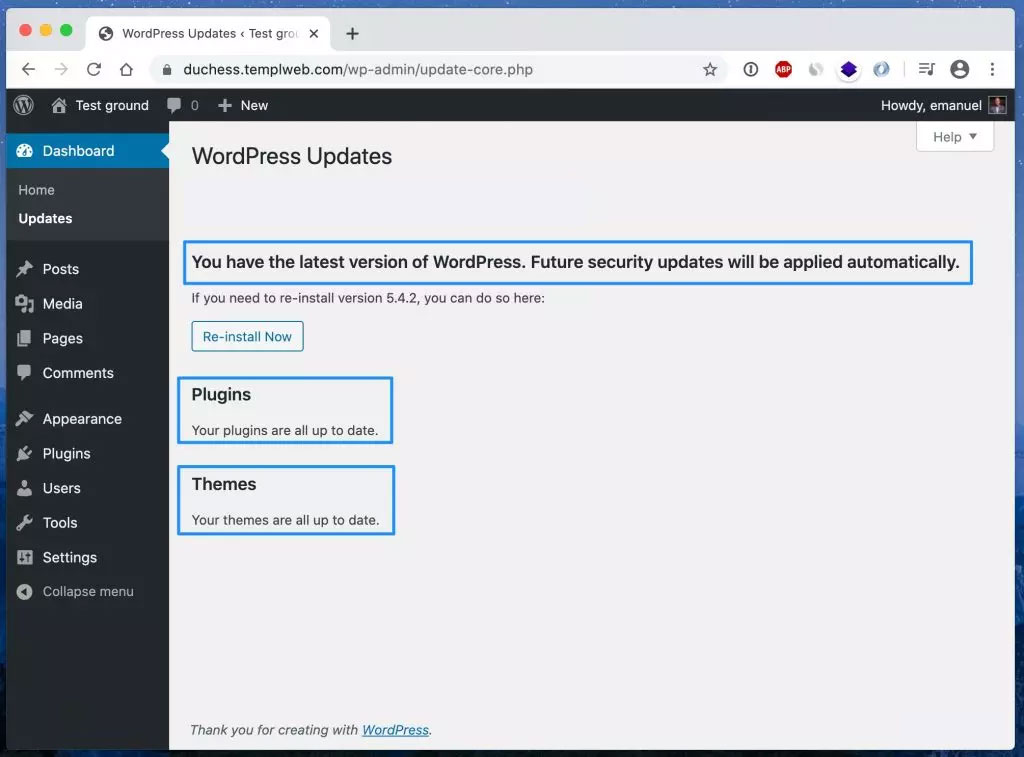
1 – Keep WordPress, plugins and themes up to date
Perhaps the most important security measure you can take is to keep your WordPress, plugins and themes up to date.
Since WordPress is an open source project, anyone can read all the underlying code and also help improve it, which of course has many benefits. But it also means that hackers and others with malicious intent can read the code and find vulnerabilities and use these to take control of other people’s websites.
Every time a security vulnerability is reported to the team behind WordPress, you can be sure that a security update will follow as soon as possible.
This means that if you do not use the latest version of WordPress, you are most likely to use a version that contains one or more known vulnerabilities. Hackers can in turn search for websites with old software and carry out targeted attacks against them.
Therefore, it is of the utmost importance to make sure you update WordPress, themes and plugins as often as you can.
Updating a website can sometimes be a little scary, especially if it is an e-commerce site, but it is often better that you yourself causes some downtime due to a bad update (provided you have backup) than someone unauthorized gaining access to it because of a known vulnerability.
Automatic updates
In WordPress 3.7, automatic updates were introduced, which allows for minor updates and security patches of WordPress to be automatically installed on your website.
You can also activate automatic updates of themes and plugins by adding the following code to your theme’s functions.php file:
add_filter( 'auto_update_plugin', '__return_true' ); add_filter( 'auto_update_theme', '__return_true' );
Verify updates in a staging environment first
For some more system critical websites that absolutely need to be up all the time and that one does not want to risk being down due to an update that went wrong, it is a good idea to always update on a staging site first and verify that updates work correctly there before updating their live website.
That way you can make sure that no surprise problems arise when updating your live website.
2 – Uninstall inactive plugins and themes
A common misconception that people have is that inactive plugins can’t have any negative impact on one’s website, but the fact is that a hacker can exploit known vulnerabilities even in plugins and themes that are inactive.
Furthermore, if you have plugins installed on your site that you do not use, it is easy to forget to update them, which of course can mean additional security risk.
We therefore recommend that you always keep the number of plugins as low as possible and uninstall plugins that you do not use, to simply deactivate them is not enough.
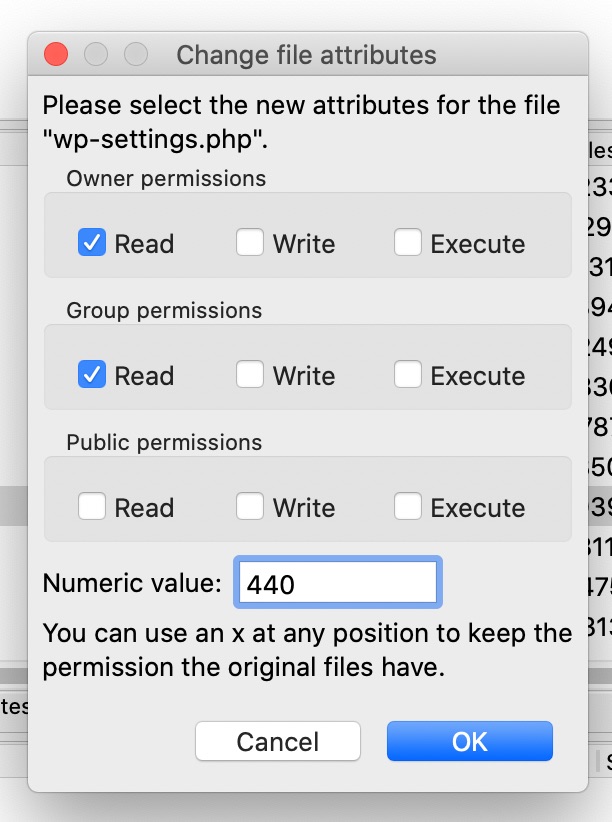
3 – Use the right (restrictive) file permissions
File permissions determine who and what can read, write, and modify the files that make up WordPress as well as anything you have installed in WordPress. If your files do not have the strictest possible file permissions in place, hackers can more easily modify your files and do infringement of your site.
File permissions are usually specified in the form of 3 digits, e.g. 755, where each digit represents a user group and what that group has the permission to do.
The first group from the left is “user” (or “owner”) rights, the second is “group” rights and the third group is “others” rights.
Simply explained, one can say that the higher the number the more rights the user has. For the interested, here is an explanation of what the different numbers actually mean:
4 = read (r) 2 = write (w) 1 = execute (x) 0 = no permission (-) Read + write + execute = 7 Read + write = 6 Read + execute = 5
All folders should have 755 or 750.
All files should have 644 or 640, except wp-config.php that should have either 440 or 400 to prevent anyone else from access it.
No folders should ever be set to 777, giving all users full rights. It should never be necessary as the PHP process is run by the file owner, and thus it can write in folders with 755.
Tight file permissions are extra important in a “shared hosting” environment, where you share server with strangers, to ensure that other users on the server cannot access your files.
How to change file permissions
Changing file permissions is easy and can be done using almost any FTP client such as the very popular and free FTP client FileZilla.
To change file permissions in FileZilla, just right-click on the file or folder you want to set the permissions for and press “File permissions …”
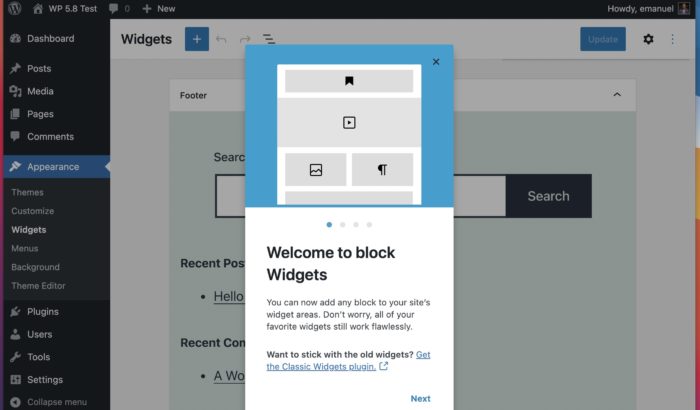
4 – Disable the built-in file editor
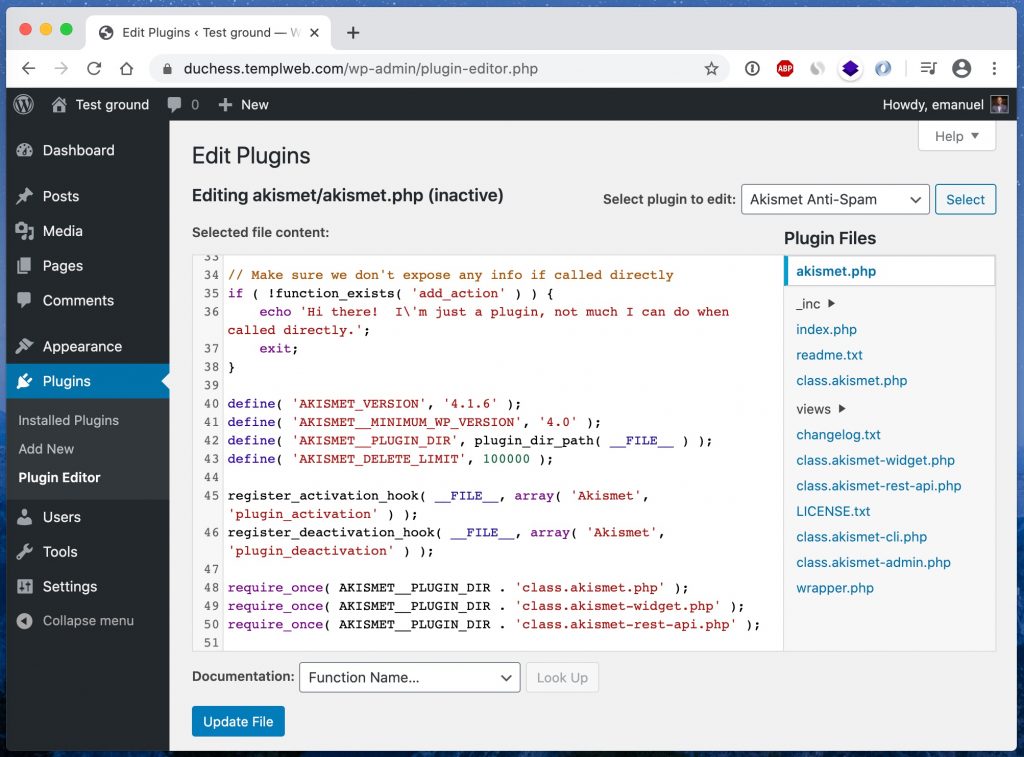
Did you know that WordPress comes with a built-in file editor for themes and plugins? It makes it easy to edit files on your website directly in WP Admin, which may be a convenience for some, but it can also pose some risks.
When the file editor is enabled, administrators can edit the code in the themes and plugins directly in the browser. It poses a potential security risk because you can easily make mistakes that cause the entire page to stop working when you make changes, and it also gives hackers quick access to all files that make up your website.
We recommend that you completely disable this built-in file editor and instead edit via files over SFTP.
The built-in file editor can be easily disabled in wp-config.php by adding the following code snippet:
define( 'DISALLOW_FILE_EDIT', true );
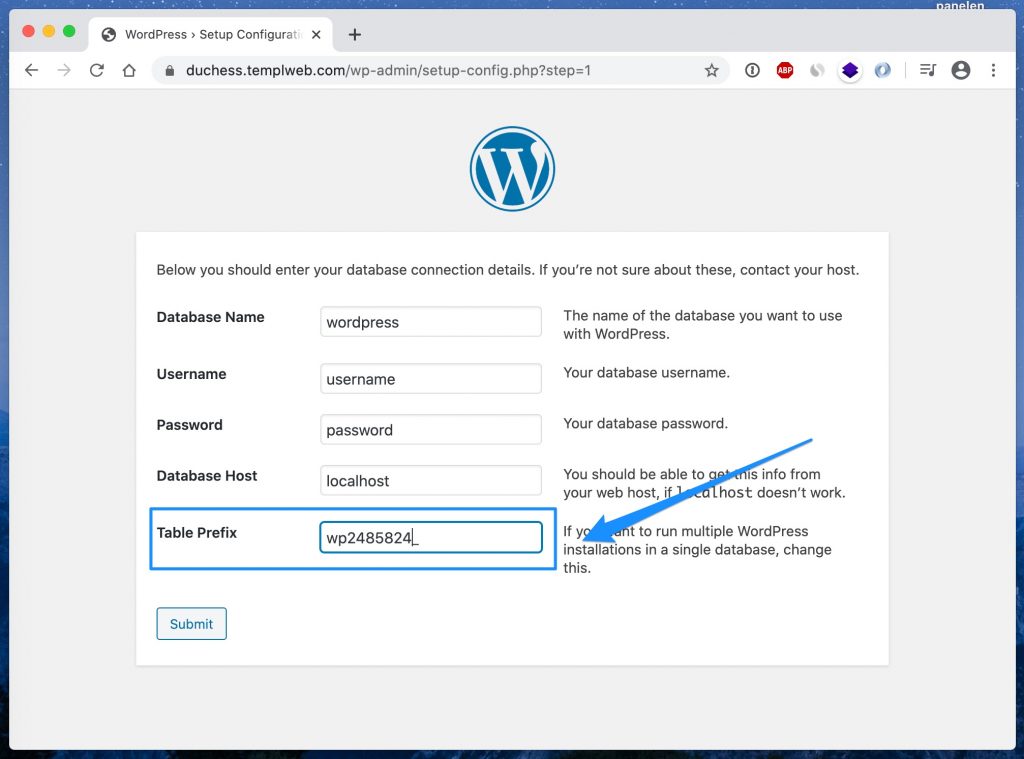
5 – Set a custom database prefix
WordPress uses a prefix in front of all tables in the database, which by deafult is wp_.
Some attacks against the database assume this particular prefix, so if you instead use another prefix you can protect your site from some attacks.
The number of attacks that assume the default prefix is unlikely to be many, and changing the prefix on an existing WordPress installation is not entirely risk-free. Therefore, we recommend only choosing another prefix if you are going to set up a new installation of WordPress, and not to change the prefix on the existing page.
6 – Use strong usernames and passwords
One of the most common ways a hacker gets into a website is by “guessing” password.
If you use simple and commonly used passwords, it is possible for unauthorized persons to easily access your website through a so called brute-force attack where the attacker submits large number of different passwords until they get in. If you use a strong password, such an attack will in reality be impossible to succeed with.
Using strong passwords may seem obvious to some, but there are still many who use very bad passwords. Security companies like SplashData and NordPass compiles lists of the most common passwords every year. The 5 most common passwords in the latest list are:
- 123456
- 123456789
- 12345
- qwerty
- password
Make sure to use a long and complex password that is randomly generated and that’s preferably exclusive to your website as well.
It is also quite common for people to use the username “admin” for their administrator account. Instead, for extra security, it is recommended to use a different username, making it even more difficult for a hacker to guess the correct username and password.
7 – Implement 2FA (Two-Factor Authentication)
2FA, or two-factor authentication, is a security process that combines two different verification methods at login: usually something you know (your password) with something you have (a unique code sent to your mobile via SMS or generated by an authentication app). This gives your website an extra layer of security that significantly reduces the risk of unauthorized access. If your password is compromised, the account remains protected thanks to the second step of authentication.
Here’s how you implement two-factor authentication on your WordPress site:
Choose a 2FA plugin: An example of a popular 2FA plugin is Wordfence Security. The 2FA plugin provides the functionality to add two-factor authentication to your WordPress site. Once installed, it can be configured for various authentication methods, including code generation from authentication apps.
Choose an authentication app: Two popular authentication apps are Google Authenticator and Microsoft Authenticator. These apps serve as the second factor in the 2FA process. When configuring your WordPress plugin for 2FA, you can choose to use these apps as your method of authentication. Typically, you scan a QR code from the WordPress plugin with the selected authentication app to link the account. The app then generates a unique code that is used for each future login.
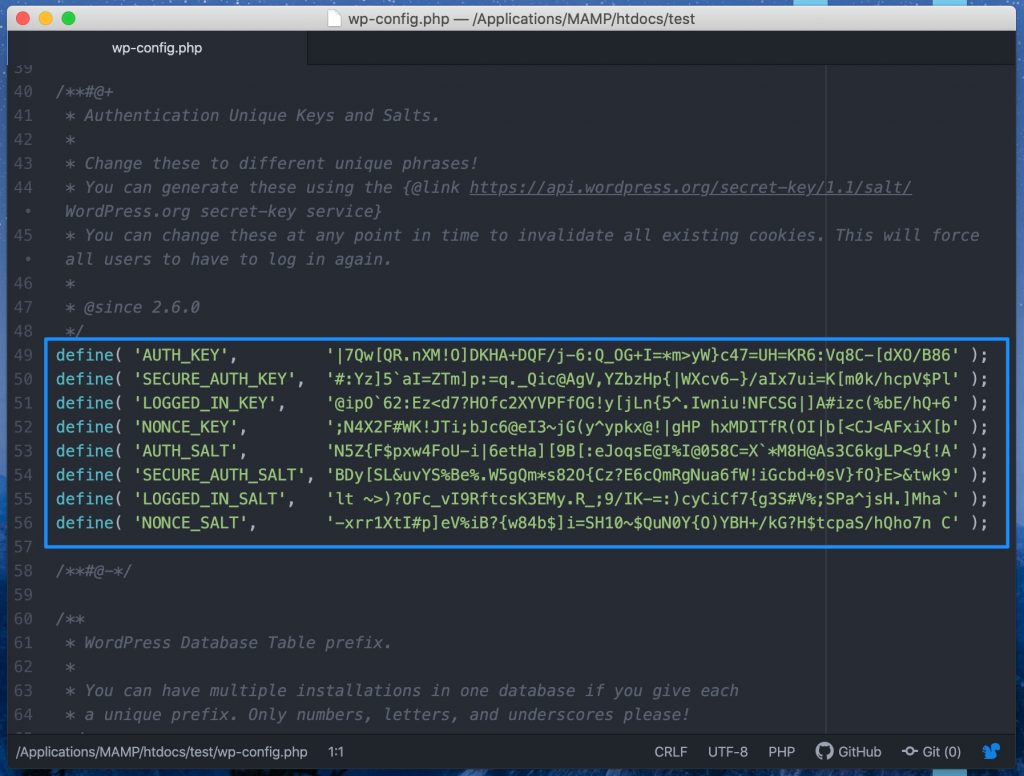
8 – Change security keys in wp-config.php
WordPress security keys are a collection of randomly generated variables that help improve the encryption of data stored in visitors and administrators cookies.
There are four different security keys: AUTH_KEY, SECURE_AUTH_KEY, LOGGED_IN_KEY, and NONCE_KEY.
When you install WordPress, these are generated in a random way and are unique to your site. However, if you have ever moved from one web host to another, or if you have taken over your website after another owner, then it may be a good idea to generate new security keys.
These can easily be replaced at any time, but it means that everyone who is logged in to your site will be logged out.
You can easily get a collection of newly generated security keys through a smart tool on WordPress.org and then paste them into wp-config.php.
9 – Disable XML-RPC
XML-RPC is a feature in WordPress that was previously used for communication between WordPress and some other systems, such as other blog networks. In recent years, however, this feature has been slimmed down as its use has been steadily declining, and the feature is planned to be completely removed in the future and replaced with WordPress’s own API instead.
Today, the actual use cases of XML-RPC are quite few. Instead, it has become a popular “tool” for hackers, as it allows testing hundreds of password combinations with a single command.
If you use Templ as a web host then XML-RPC is already disabled from the start, and if you use any other web host then it is relatively easy to disable that function in other ways.
You can either disable XML-RPC using a plugin, or by pasting some code into one’s theme’s functions.php file:
add_filter( 'xmlrpc_enabled', '__return_false' );
.. or even better is to disable it using .htaccess:
<Files xmlrpc.php> order deny,allow deny from all </Files>
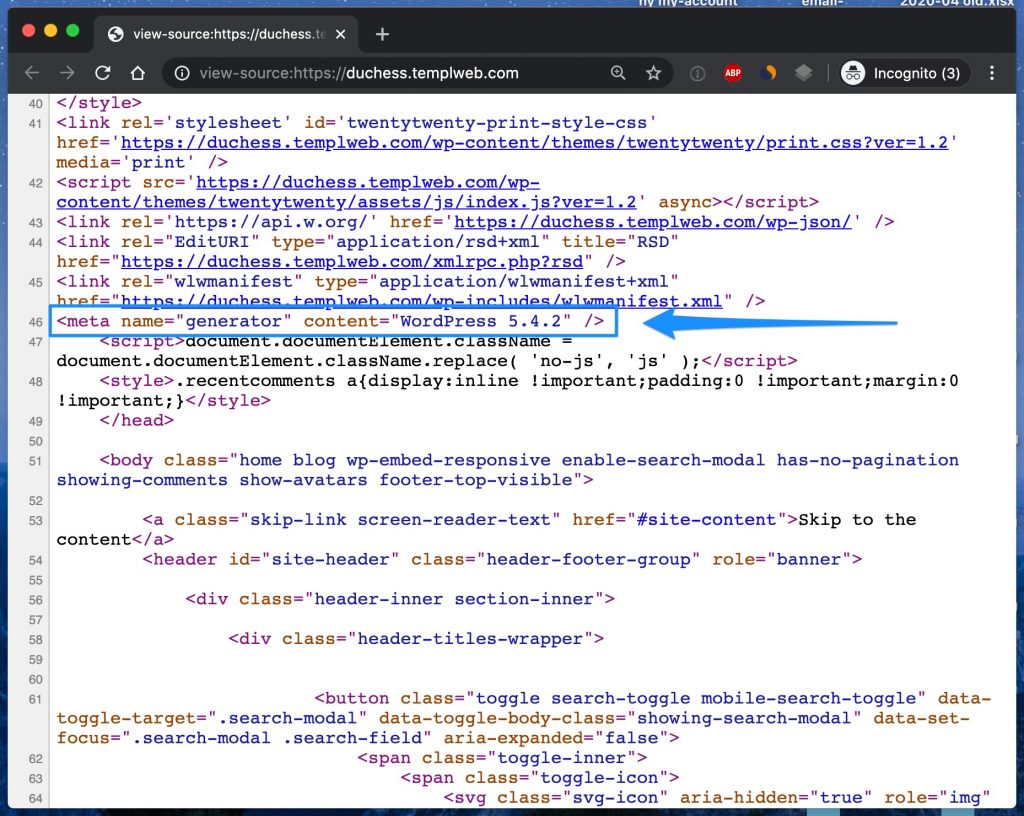
10 – Hide what WordPress version you are using
Which version of WordPress that are used on your site is usually visible in your site’s HTML code, so if you have an old version of WordPress with known vulnerabilities then it is very easy for a hacker to access that information.
Although we of course recommend that you always run the latest version of WordPress, it can still be a good idea to hide the version number for your visitors. The less outsiders know about your WordPress installation, the harder it is to make targeted attacks against it.
It’s easy to hide WordPress version with a little code in functions.php:
function wp_version_remove_version() {
return '';
}
add_filter('the_generator', 'wp_version_remove_version');
11 – Use SSL and HTTPS
Although SSL has become something of a given thing today, it does not hurt to once again emphasize the importance of SSL if you want a secure website.
With an SSL certificate you can use the encrypted protocol HTTPS instead of old and unencrypted HTTP. This means that when you fill in, for example, a login form on a page with HTTPS, the information is encrypted, including passwords and other sensitive information, making it impossible for anyone else to eavesdrop.
Although the biggest advantage of SSL is security, it is also today strongly associated with SEO benefits (because Google and others prefer HTTPS over HTTP), increased visitor trust.
Having an SSL certificate and running your site over HTTPS is definitely a must.
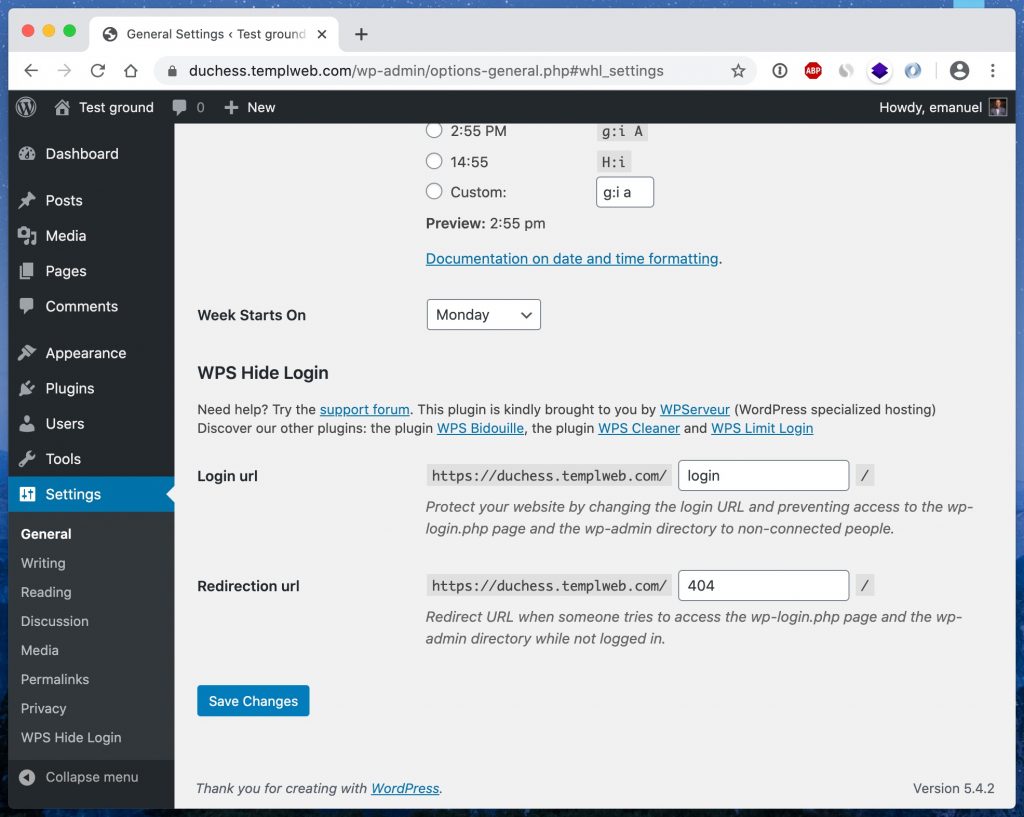
12 – Change WP Admin URL
All WordPress sites initially uses one and the same URL for WP Admin, namely example.com/wp-admin. One potential problem with this is that everyone knows of this address, including bots and hackers.
By changing the URL to WP Admin you can make a site less vulnerable to attacks.
You can easily change the address of WP Admin by using the WPS Hide Login plugin. Which we also describe in detail how to set up in another blog post.
It’s important to keep in mind that this is not a solution to all problems, but it can clearly be one way to make it more difficult for hackers to access your site.
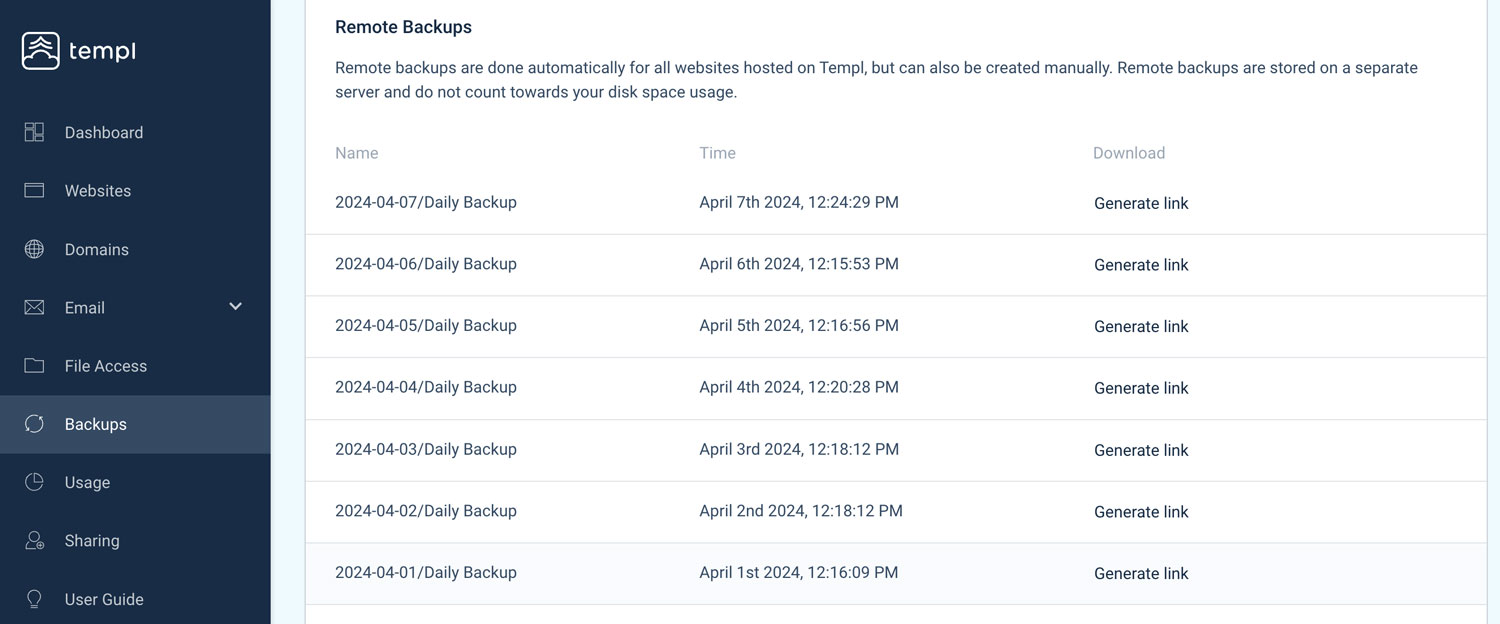
13 – Make sure to take daily backups
Backing up your website is of course not an action that prevents it from suffering any kind of attack, but on the other hand it is absolutely invaluable to have in case disaster strikes and you need to be able to “rewind the tape” to save your website.
No matter what preventative measures you take, your website will never be 100% secure. Therefore, one should always make sure that backups of one’s website are taken on a regular basis.
Most web hosting companies in the premium segment take daily backup of all websites, as do we at Templ. In case your web host does not offer automatic backups, then it is quite easy to solve on your own by using for example the plugin UpDraft, but you should then keep in mind that a backup plugin will affect your website’s performance and use much of the storage space you pay for in your web hosting plan.
14 – Choose a secure hosting solution
When it comes to security and WordPress, there are many factors at play that sit deeper than the website itself. There are also a lot of security measures that need to be taken at the server level, of which your web host is responsible. At Templ, we take security very seriously and always have a safety mind in everything we do.
It is very important to choose a web host that you can really trust, or that you yourself have extremely good knowledge of security if you choose to place your website on a VPS and thus bear the entire responsibility for security yourself.
It is also important to know that different web hosting companies have vastly different policies for what they do when a website is hacked. Some web hosts simply shuts down websites that have been hacked and don’t want to know of them, while we at Templ offer free help to rescue hacked website.
A web host that takes security seriously often has:
- A firewall that protects against various attacks
- Latest version of PHP, MySQL and other software
- Daily backups
- Support available around the clock
- 24/7 monitoring of all websites
- And a number of other advanced features for better security
Final words
In conclusion, it is worth repeating that WordPress itself is very secure, but that it is important to keep everything updated and that you use common sense.
It is also important to remember that there are many factors that affect the security of one’s website that is “deeper” than WordPress itself. Therefore, it is important that you either have a very good understanding of IT security yourself or that you choose web hosting that takes security seriously.
Daily backups of one’s website are also an absolute must so that you have something to fall back on, should a serious accident occur.
If you have any questions about WordPress security then you are welcome to ask us in the chat here on this page or to post in the comment box below.
Good luck! 🙂